Software development blog
Development of interaction with mobile devices user – key principles
- 19.10.2016
- Tatiana Kir
There is one the most vital thing to be remembered developing a mobile application is it’s being both useful and intuitively comprehensible. If the application is not beneficial, it means that any practical value and motivation to use it ...
IoT Achilles Heels
- 18.10.2016
- Alexa Klimow
Ancient Greece brought to life many metaphors and comparisons to our language as well as various set expressions. The term Achilles Heel is used to some particular weak spot something or somebody might have because according to the Greek legend ...
B2B, B2C vs H2H business models in IT development
- 17.10.2016
- Anton Kulich
The three letter-number-letter abbreviations in the title of the article may seem to be mere labels with not much significance behind them. However, these are the terms that subconsciously invoke certain associations in people, and shape their ...
Recent release of iPhone 7: what is in it for mobile app developers and users
- 14.10.2016
- Anton Kulich
The official presentation of new Apple products is always associated with massive hype, addicted fans standing in lines since midnight, naysayers criticizing the innovations and experiments introduced, and developers curious about the ...
Case Study: A huge platform for 200+ sites as an answer how to sell tickets online by the more proper way
- 13.10.2016
- Margaret Geras
Haven’t you ever asked yourself how to sell tickets online in the more proper way? We’ve implemented this idea. Our novelty is about to be accomplished. The project represents a big base of addresses, proposals, and has personal ...
BlackBerry Officially Ends Smartphone Production
- 13.10.2016
- Margaret Geras
BlackBerry has announced that it will cease the development and production of mobile phones. This is stated in the company’s financial report for Q2 of the fiscal year 2017 (it ended on the 31 August 2016). Now the company will devote its ...
How mobile e-commerce contributes to retail in business
- 12.10.2016
- Tatiana Kir
There are two main targets of modern retail businessmen that will increase the profit and make the work more comfortable. The first one is a constant increase in sales; the second one – a possibility to control the work of the employees and ...
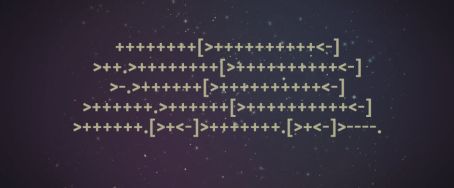
Brainfuck: a Programming Language or a Joke?
- 11.10.2016
- Margaret Geras
There are a great number of esoteric programming languages in the world, and the most famous one is brainfuck. To make it sounds better, you also may call it BF or b*fuck, but the essence will stay the same – it is a brain fuck. Being extremely ...
Microsoft represented a protective technology Windows Defender Application Guard for Edge web-browser
- 10.10.2016
- Tatiana Kir
Microsoft has recently announced special measures taken to be protected from malicious software and cyber-attacks based on the mechanism of virtualization Hyper-V. With the release of Windows 10, the company represented the so-called environment ...